Untitled Document
 |
|
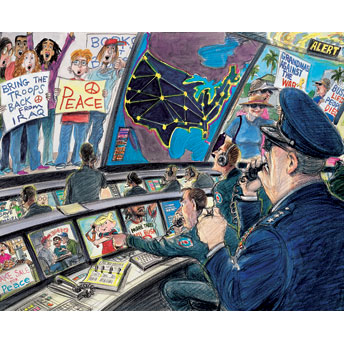
Illustration by Victor Juhasz
|
The military has built a vast domestic-intelligence network to fight
terrorism -- but it's using it to track students, grandmothers and others protesting
the war
Last October, before the public learned that president Bush had secretly ordered
the National Security Agency to eavesdrop on Americans without a court order,
the Pentagon approached the Senate intelligence committee with an unprecedented
request. Military officials wanted the authority to spy on U.S. citizens on
American soil, without identifying themselves, in order to collect intelligence
about about terrorist threats. The plan was so sweeping, according to congressional
sources who reviewed it, that it would have permitted operatives from the Defense
Intelligence Agency to spy on dissidents by posing as peace activists and infiltrating
anti-war meetings.
Senators on both sides of the aisle refused to go along with the plan. "The
Department of Defense should not be in the business of spying on law-abiding
Americans -- period," said Sen. Ron Wyden, a Democrat from Oregon. In closed-door
deliberations, the intelligence committee blocked the request.
In fact, however, the Pentagon has already assembled a nationwide domestic
spying machine that goes far beyond the National Security Agency's warrantless
surveillance of telephone and e-mail traffic. Operating in secret, the Defense
Department is systematically gathering and analyzing intelligence on American
citizens at home -- and a new Pentagon agency called Counterintelligence Field
Activity (CIFA) is helping to coordinate the military's covert efforts with
federal, state and local law enforcement agencies.
Those responsible for the military's new spy network insist that it is aimed
at preventing another attack by Al Qaeda. "The premise is that there needs
to be a nexus to foreign terrorism," says David Burtt, CIFA's director.
"In the wake of 9/11, there was a lot of criticism about the ability to
collect dots and connect dots."
So far, the military's efforts at domestic spying have caught few, if any,
terrorists. But the Pentagon has tracked the activities of anti-war activists
across the country who have staged peaceful demonstrations against military
bases and defense contractors such as Halliburton. Traditionally restricted
to action overseas, America's armed forces -- including the National Guard --
are now linked in a growing domestic spying apparatus which, thanks to technology,
has far greater power than the Army units that conducted a massive operation
to infiltrate, disrupt and destabilize Vietnam and civil rights protests during
the 1960s and '70s. "We are deputizing the military to spy on law-abiding
Americans in America," said Wyden. "This is a huge leap without even
a congressional hearing."
* * * *
Intelligence gathered by the military runs into and out of the U.S. Northern
Command in Colorado Springs, Colorado. Here, beneath the snow-covered summit
of Pike's Peak, the Defense Department has set up its first command dedicated
to homeland security in a gleaming new $90 million facility. Before Northcom
was established in 2002, the facility was best known as the home of the North
American Aerospace Defense Command, the ultra-high-tech war room depicted in
the movie WarGames, where sharp-eyed military personnel spent the Cold War watching
for a nuclear attack by the Soviet Union.
Nowadays, the place is more like a real-life version of the counterterrorism
unit on 24. Judging from the bustle of activity at Northcom, anti-terrorism
is good for business. The corridors are filled with dust from construction and
the smell of paint, and a brand-new wing is nearly ready to open. Over the past
four years, Northcom has doubled in size and now boasts a staff of 1,200 and
an annual budget of $93 million.
At the center of the operation is a core group of 300 intelligence analysts
and staff who inhabit Northcom and its state-of-the-art facility, called the
Combined Intelligence Fusion Center. "Intelligence fusion" is a spy
master's term of art that refers to melding together data from all points --
including intelligence agencies, the armed forces, law enforcement and other
sources -- and analyzing all the seemingly disparate information for patterns.
"The fusion and analysis that these kids do is different than anything
I've seen in forty years," says Adm. Timothy Keating, the commander of
Northcom.
The intelligence streaming into the center can be anything from highly polished
analyses from the CIA and FBI to the military's own alerts and warnings. At
the bottom are Suspicious Activity Reports (SARs) filed by many government agencies,
which are often little more than rumors based on unfounded information -- a
financial officer who notes an odd money transfer or a military spouse who spots
a suspect individual near a base. More official are Threat and Local Observation
Notices (TALONs), part of a surveillance program started by the Pentagon in
2003. More than 15,000 TALONs have been collected so far, from sources such
as soldiers manning gates outside military bases, law-enforcement agencies,
local businesses and the media. The SARs and TALONs -- along with intelligence
from the armed forces, such as the U.S. Air Force program known as Eagle Eyes
-- are eventually integrated into a single intelligence database called JPEN,
for the Joint Protection Enterprise Network.
In its homeland-security role, Northcom has mobilized troops for hundreds of
events since 2002, including the Super Bowl, the Daytona 500, Boy Scout jamborees
and the presidential inauguration. The sixty-four members of its instant command
center, including an intelligence team that can be mobilized in hours, have
been sent into action at special events nine times in the past two years. In
addition, scores of federal agencies -- from the CIA and FBI to the Coast Guard
and FEMA -- have officials based at Northcom to coordinate their work. "We're
fully integrated with the Special Operations Command," says Maj. Gen. Richard
Rowe, Northcom's director of operations. "We have people who've done operations
from a Special Ops perspective."
Inside Northcom's operations center, where wall-size screens flank rows of
computer terminals linked to federal agencies, military analysts monitor everything
from the president's travels to routine air traffic. A placard in the war room
lists fourteen events that merit immediate attention -- "we call them 'wake
me up in the middle of the night' stuff," says Col. Bob Felderman of Northcom
operations. Adds another Northcom official, "We get reports if somebody's
pounding on a cockpit door in flight, or there's a drunk passenger, or somebody's
taped a note in an airplane restroom." But the list also includes a category
for "civil disturbances of more than 1,000 persons" -- a directive
broad enough to include an anti-war demonstration or anti-globalization protest.
Keating, a gray-haired commander who led the U.S. Fifth Fleet, insists that
Northcom does not spy on Americans. "We are not allowed to gather intelligence
on U.S. persons unless there is a clearly defined, well-understood terrorist
nexus," he says.
Ever since 1878, when the Posse Comitatus Act barred the U.S. military from
taking part in law enforcement, the responsibility for domestic security has
traditionally resided with the police and the FBI. The Defense Department, for
the most part, has been confined to protecting U.S. military bases. But shortly
after September 11th, the Pentagon began muscling in on the FBI's turf. In 2002,
in a move that received little public attention, the Bush administration created
Counterintelligence Field Activity and charged the new agency with consolidating
all Pentagon intelligence to "protect DOD and the nation against espionage,
other intelligence activities, sabotage, assassinations and terrorist activities."
The agency got another boost last year when a commission appointed by Bush
urged that CIFA be empowered to collect and analyze intelligence "both
inside and outside the United States." Three of the commission's consultants,
it turns out, were employees of MZM -- one of CIFA's primary contractors --
and federal prosecutors are now looking into whether Pentagon personnel have
committed crimes in steering CIFA contracts to MZM. Nevertheless, the president
agreed last October to significantly broaden the agency's mission, giving it
the authority to actually direct military intelligence operations. From a small
unit designed as a clearinghouse for reports, CIFA was transformed overnight
into a major arm of domestic intelligence. Both its budget and its staff, thought
to be in excess of 1,000 people, are classified.
According to a Defense Department strategy paper, military spying encompasses
not only "defense critical infrastructure" -- highways, bridges, communications
facilities, chemical plants and nuclear reactors -- but also the "defense
industrial base," which the paper describes as "a worldwide industrial
complex with capabilities to perform research and development and design, produce,
and maintain military weapons systems, subsystems, components or parts to meet
military requirements." In other words, the Pentagon sees itself as defending
the entire military-industrial complex -- a mission broad enough to include
intelligence on virtually any conceivable threat.
* * * *
It didn't take long for the pentagon to begin using its new powers to collect
intelligence on anti-war groups. In December, NBC News reported that CIFA had
collected dozens of incident and threat reports on peace activists and other
nonviolent organizations that have nothing to do with terrorism. By matching
the unnamed groups in the news reports to specific activities of activists nationwide,
the American Civil Liberties Union discovered that the military's spying effort
had ensnared the American Friends Service Committee, United for Peace and Justice,
and Veterans for Peace, as well as local anti-war groups from Florida to California.
A group at University of California Santa Cruz called Students Against the
War was included in CIFA's terrorism database in April 2005, when it staged
a protest against military recruiters on campus. Although the protest was peaceful,
a TALON report called the demonstration a "threat," an assessment
that CIFA deemed "credible." A Florida group called the Truth Project
ended up in the database in November 2004, when they gathered at a Quaker meetinghouse
to plan a protest against high school recruiting by the military. Five months
earlier, ten peace activists in Texas merited a TALON report for donning papier-m?ch?
masks and handing out peanut-butter sandwiches to highlight "war profiteering"
outside the offices of Vice President Dick Cheney's former firm, the defense
contractor Halliburton.
In May 2005, a California group called the Raging Grannies ran afoul of military
spies when it helped organize a peaceful Mother's Day demonstration to protest
the war in Iraq. Unbeknownst to them, their action was brought to the attention
of a new intelligence unit at the California National Guard -- a program that
went by the cumbersome title of Information Synchronization, Knowledge Management,
and Intelligence Fusion. According to internal e-mails, the Guard forwarded
information about the protest "to our Intell folks who continue to monitor."
Asked why the Guard was spying on the Grannies, a spokesman suggested that
terrorists might try to take advantage of the activists. "Who knows who
could infiltrate that type of group and try to stir something up?" Lt.
Col. Stan Zezotarski told reporters. "After all, we live in an age of terrorism,
so who knows?"
Joe Dunn, a California state senator, was having none of it. He launched an
investigation and helped force the Guard to shut down its intelligence center.
"What got us to the point of the National Guard setting up units in which,
at least in California, they start down the path of domestic spying?" he
asks. "Our fear is that this was part of a federally sponsored effort to
set up domestic surveillance programs in a way that would circumvent the Posse
Comitatus Act."
The ACLU, which is demanding more information about CIFA's activities, cites
a "broad and disturbing pattern" in the military's intelligence gathering,
saying the efforts are being used to target legitimate protesters. "The
chilling effect of this may be the most significant," says ACLU staff attorney
Ben Wizner. "There is a real danger when the military is seen as being
used as part of the administration's political goals."
According to Denice Denton, the chancellor at Santa Cruz, the military's covert
intelligence operation is already deterring dissent. "It has intimidated
people," she says. "I spoke to one of the students involved, and she
feels intimidated about speaking openly because she is being watched. Students
wonder, 'How was this information being collected? Were people standing behind
a tree?' "
Some of the military intelligence, in fact, appears to be based on very little
intelligence. "These reports are nothing more than a gossip and rumor index,"
says Christopher Pyle, a former Army intelligence officer who exposed some of
the abuses by military spy agencies in the 1960s. "A lot of them are filed
by paranoid housewives and rabid, retired colonels with nothing better to do
than spy on the people around them."
With the military spying on peace groups, some activists say they are on the
lookout for moles within their own ranks. Ray Del Papa, who attended the Truth
Project meeting in Florida, told reporters that he believes government agents
infiltrated the organization. "You could pretty much pick out who are the
infiltrators," he said. "It gets you mad. It is wrong for anyone from
the government to have to spy on U.S. citizens."
No one disputes that the Pentagon has a responsibility to protect its facilities
and personnel. But its broad definition of "terrorism" could easily
lead it back into the business of targeting legitimate protesters. In the late
1960s, more than 1,500 Army personnel tracked a wide range of dissident groups
and monitored every demonstration involving more than twenty people, amassing
files on more than 100,000 Americans.
The Pentagon has apologized for the latest abuses and pledged to clean up its
act. Robert Rogalski, acting deputy undersecretary of defense for counterintelligence
and security, says a complete review of CIFA's database is under way, adding
that any data on dissidents was included by mistake. "We've laid our dirty
laundry on the table, we recognize that mistakes were made, and we've done the
right thing," he says. "It did cause us to realize that we have to
sharpen the focus."
But it may be hard to undo the damage. By law, TALON reports that do not warrant
further investigation are supposed to be purged from all databases after ninety
days. Yet the information is shared with so many agencies, there is simply no
way for citizens to know that their names have been cleared. "It's impossible
to know how many databases there are," says Jim Harper, an information-policy
specialist at the conservative Cato Institute in Washington, D.C. "And
every other week, databases are being combined."
The broader threat is that military spies will gradually expand their anti-terrorist
mission to include more and more ordinary citizens. "The danger is that
we create an apparatus for spying -- and that becomes the essential apparatus
of a police state," says Pyle, the former intelligence officer. "It
goes from clipping articles to sending people out to watch protesters to taking
video and sending it back to the Pentagon. If some kids knock down a power line
somewhere, soon they'll be looking at every member of Earth First! and the Earth
Liberation Front." The military's intelligence gathering got out of hand
thirty-five years ago, Pyle observes. "And my sense is," he says,
"the bureaucracy forgets stuff like that."

